Category: Cyber Security
-

I Built an AI-Powered Malware Analysis Tool. Here’s What It Does.
If you’ve ever done malware analysis, you know the feeling. You’ve got a suspicious file, and you know the answers are in there somewhere — what it does, how it hides, where it phones home. But getting to those answers means loading the file into one tool for the structure, switching to another for the…
-
14 Malware Samples, 289 Tools, and What I Learned Building an AI-Driven Analysis Platform
When I first started building what would become Arkana, I had one question: could it actually handle real malware? Not toy samples or contrived demos — proper, nasty, in-the-wild stuff that would give a seasoned analyst a headache. So I threw 14 different samples at it and let it loose. Here’s what happened. The Test…
-
From PeMCP to Arkana: 289 Tools, One AI-Driven Malware Analysis Platform
Back in October, I introduced a couple of tools I’d been building — ProcmonMCP and the PeMCP Toolkit. If you read that post, you’ll know the whole thing started from a simple frustration: spending far too many hours manually sifting through binary analysis data, knowing the answer was right there if only I could get…
-
How I’m Teaching Myself Reverse Engineering (With a Tool I Built)
I’ll be honest — for a long time, reverse engineering scared me a bit. I could muddle through the basics, but the moment I hit a wall of assembly code or a packed binary with five layers of encryption, I’d feel completely out of my depth. The resources out there are either aimed at total…
-

A Better Way to Analyse: Introducing My New Tools, ProcmonMCP & the PeMCP Toolkit
If you’ve ever worked in digital forensics or malware analysis, you know the feeling. You’re staring at a screen, buried under a mountain of data. It might be a Procmon trace with millions of events, or a packed executable that refuses to give up its secrets. I’ve lost count of the hours I’ve spent manually…
-

Cisco CVE-2024-20295 – “Fox in a box” CLI Command Injection Disclosure
Cisco Integrated Management Controller CLI Command Injection Vulnerability – Disclosure
-
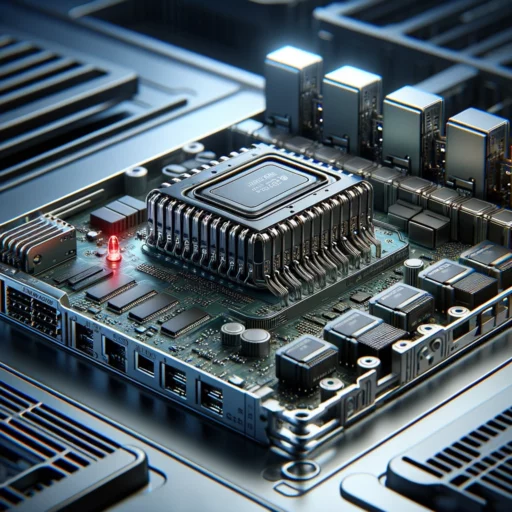
Rooting a Cisco IMC for peace and power!
A brief introduction TL;DR: In a home lab project, a Cisco UCS server was acquired to replace an older Dell server. However, the Cisco server’s fans were excessively loud and power-intensive. By gaining root access to the server’s Cisco Integrated Management Controller (IMC), which is similar to HP’s iLO or Dell’s iDRAC, it was possible…